When to conduct penetration tests about Android applications, this is a small piece to help you.
It is easy to decompile and repack android apps (apk).
The following list describes some android terms:
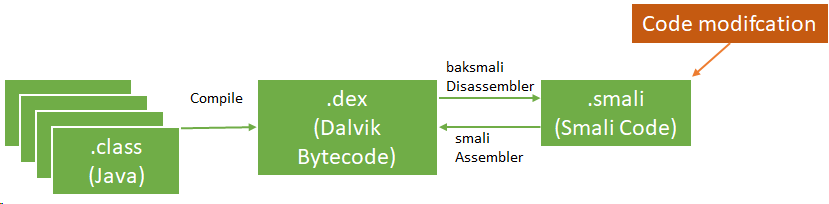
- Smali disassembled Java opcodes in textual format generated by baksmali, a DEX format disassembler
- App Manifest: XML file that provides essential app information
Basic static analysis provides a general understanding of the mobile application's structure. the apktool can help to decompile the app's resources.
$apktool d -o ./sample sample.apkThe apk could contains meta information in AndroidManifest.xml file, and other files as per below:
- AndroidManifest.xml
- classes.dex
- res/
- lib/
- META-INF
We could update source codes on in the disassembled class files (smali).
There are few methods to update smali files.
- Manually add/edit/remove smali code. We should learn about smali code. This URL may be useful. In this case, JD GUI and jadx-gui are useful tools.
- You build new android app with your android java code, and disassemble the apk to extract the smali code.
After update the smali code, you could build an updated apk using apktool.
$apktool b -o sample_new.apk ./sampleNext, we could create key and sign.
$keytool -genkey -v -keystore resign.keystore -alias alias_name -keyalg RSA -keysize 2048 -validity 10000
$jarsigner -verbose -sigalg SHA1withRSA -digestalg SHA1 -keystore resign.keystore sample_new.apk alias_name
If you know how to use smali language, you can modify apk much easier.
Reference:
1. OWASP MASVS - https://github.com/OWASP/owasp-masvs/releases/
No comments:
Post a Comment